2.1
Types of Digital Watermarking Techniques
2.1.1
Visible and Invisible Watermarking
Watermarking techniques can be categorized as visible or invisible, depending on their perceptibility to the human eye. Visible watermarks are easily discernible and are commonly used for branding or copyright protection purposes. On the other hand, invisible watermarks are imperceptible and are employed for more discreet applications, such as content authentication and tamper detection [1].
Interesting
Example: Visible Watermarking for Stock Photos
Imagine you're a professional photographer named Sarah, who specializes in capturing stunning landscapes and nature photos. You decide to share your work on a popular stock photo website to earn some extra income. However, you're concerned about protecting your intellectual property and preventing unauthorized use of your images.
Imagine you're a professional photographer named Sarah, who specializes in capturing stunning landscapes and nature photos. You decide to share your work on a popular stock photo website to earn some extra income. However, you're concerned about protecting your intellectual property and preventing unauthorized use of your images.
To address this issue, you opt for visible watermarking. Before uploading your photos to the stock photo platform, you embed a semi-transparent logo or text overlay onto each image, clearly displaying your name or business name. This visible watermark acts as a deterrent, discouraging potential users from using your photos without proper licensing or attribution. Now, when someone browsing the stock photo website comes across your images, they will immediately see the visible watermark, indicating that the photos are protected and owned by you. If they wish to use your photos for their projects, they will need to purchase the appropriate license and obtain the watermark-free version from the stock photo platform.
+
Fig. 2: Example of a photo with visible digital watermark
By employing visible watermarking, you can safeguard your intellectual property, assert your ownership, and ensure that you receive proper compensation and recognition for your work as a photographer.
Interesting
Example: Invisible Watermarking for Sensitive Documents
Let's consider another scenario involving a law firm handling sensitive legal documents. The firm deals with confidential client information, contracts, and legal agreements that require the highest level of security and authenticity. To protect these sensitive documents from tampering and unauthorized access, the law firm implements invisible watermarking. Before distributing any digital copies of the documents, a unique and imperceptible watermark is embedded into each file. This invisible watermark contains essential information, such as the document's origination date, the client's identification number, and a secure hash code.
Now, imagine a situation where a client disputes the authenticity of a legal agreement they signed with the law firm. The law firm can easily verify the document's integrity by extracting the invisible watermark and comparing it with their secure database records. If the extracted watermark matches the original record, it proves that the document has not been tampered with since its creation.
Furthermore, if an unauthorized individual gains access to confidential documents and attempts to leak or distribute them, the invisible watermark can help trace the origin of the leak. The law firm can analyze the extracted watermark to identify the specific client or employee associated with the compromised document, aiding in the investigation process.
+
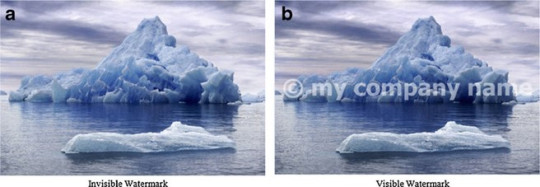
Fig. 3: Difference between Invisible watermark (a) and Visible watermark (b)
By leveraging invisible watermarking, the law firm can ensure the authenticity, confidentiality, and traceability of their sensitive legal documents, providing an additional layer of security and trust in their services.
These are just a couple of examples to illustrate the practical applications of visible and invisible watermarking. We can continue exploring more examples for other watermarking techniques, such as spatial and frequency domain watermarking, hybrid watermarking, and reversible watermarking, in a similar storytelling style to make the document more engaging and informative.
Watermarking techniques can also be classified based on the domain in which the watermark is embedded. Spatial domain techniques directly modify the pixel values of the host image or video frame to embed the watermark.
These methods are relatively simple and computationally efficient but may be less robust against certain attacks.
Interesting
Example: Spatial Domain Watermarking for Social Media Images
Picture a social media influencer named Alex who regularly shares his travel photos on various platforms like Instagram and Facebook. Alex has built a substantial following, and his stunning images often go viral. However, he notices that some of his photos are being used by other accounts without his permission, often with the watermark cropped out.
To combat this issue, Alex decides to employ spatial domain watermarking. Before posting his images on social media, he uses a watermarking software that embeds a hidden watermark directly into the pixel values of the image. This watermark is invisible to the naked eye and does not affect the visual quality of the photo.
Now, whenever someone attempts to use Alex's images without his consent, he can easily prove his ownership by extracting the hidden watermark. Even if the unauthorized user crops or resizes the image, the watermark remains intact within the pixel values, providing robust proof of originality.
Note
Moreover, if Alex suspects that one of his watermarked images has been used without permission, he can use a reverse image search tool to locate the unauthorized copies online. The spatial domain watermark acts as a unique identifier, making it easier to track and identify the misused images across different platforms.
+
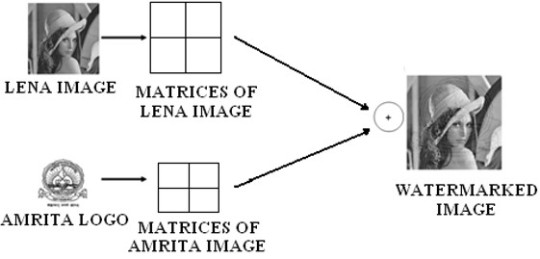
Fig. 4: Example of Spatial Domain Watermarking with two images
By implementing spatial domain watermarking, Alex can protect his intellectual property, maintain control over his creative work, and deter unauthorized use of his popular travel photos on social media.
Frequency domain techniques, on the other hand, transform the host image or video frame into a spectral representation before embedding the watermark. Common transformations used include Discrete Cosine Transform (DCT), Discrete Wavelet Transform (DWT), and Discrete Fourier Transform (DFT). Frequency domain techniques are generally more robust against attacks but may be more computationally intensive [2].
+
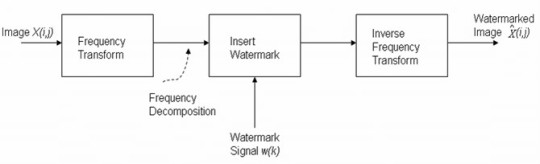
Fig. 5: General principle of Frequency domain watermarking
Interesting
Example: Frequency Domain Watermarking for Online Video Streaming
Consider a video streaming platform called StreamSecure that hosts a wide range of movies, TV shows, and original content. The platform wants to ensure that their videos are not illegally downloaded, redistributed, or tampered with, as it could lead to revenue losses and copyright infringement issues. To address these concerns, StreamSecure incorporates frequency domain watermarking into their video files. Before uploading the videos to their platform, they apply a discrete cosine transform (DCT) to the video frames and embed a watermark in the frequency domain. This watermark contains essential information, such as the video's unique identifier, the streaming platform's name, and a timestamp.
When a user streams a video from StreamSecure, the watermark remains imperceptible and does not affect the viewing experience. However, if someone attempts to record the video using screen capture software or other means, the watermark persists in the copied version.
In case StreamSecure discovers an unauthorized copy of their video circulating on the internet, they can extract the embedded watermark from the pirated version. The watermark information helps them identify the specific video, the time it was streamed, and potentially the user account associated with the illegal recording. This evidence can be used to take legal action against the infringer and protect StreamSecure's copyrighted content.
+
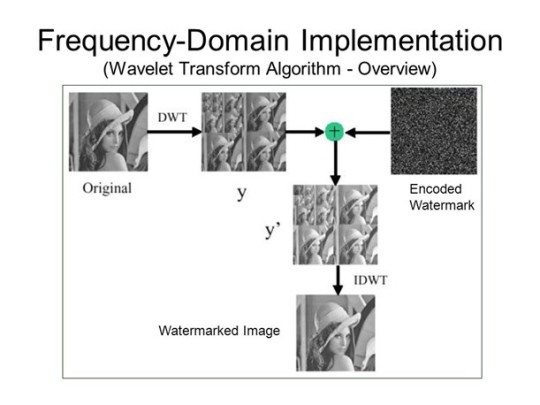
Fig. 6: Example of Frequency domain watermarking
Note
By employing frequency domain watermarking, StreamSecure can safeguard their video content, deter piracy, and maintain the integrity of their streaming platform.
2.1.3
Hybrid Watermarking
Hybrid watermarking techniques combine the strengths of both spatial and frequency domain methods. These techniques often employ a two-stage embedding process, where the watermark is first embedded in one domain and then further processed in another domain. Hybrid approaches aim to achieve a balance between robustness and imperceptibility [3].
Interesting
Example: Hybrid Watermarking for Feature Films
Imagine a major film studio called CinemaWorks that produces high-budget feature films. The studio invests significant resources into creating visually stunning movies with cutting-edge special effects. However, they face the constant threat of piracy, where their films are illegally recorded, copied, and distributed online, leading to substantial financial losses.
To combat this issue, CinemaWorks implements hybrid watermarking techniques. They combine both spatial domain and frequency domain watermarking to create a robust and secure watermark for their films. The watermarking process begins in the spatial domain, where a hidden watermark is embedded directly into the pixel values of the video frames. This watermark contains information such as the studio's name, the film's title, and a unique identifier.
Next, the watermarked video undergoes a frequency domain transformation, such as the discrete wavelet transform (DWT). In the frequency domain, an additional watermark is embedded, providing an extra layer of security. This frequency domain watermark may include more detailed information, such as the date and time of the film's release, the distribution region, and an encrypted signature.
The hybrid watermarking approach makes it extremely difficult for pirates to remove or tamper with the watermark without significantly degrading the video quality. Even if they attempt to compress or resize the pirated copy, the watermark remains intact in both the spatial and frequency domains.
In the event of a piracy incident, CinemaWorks can extract the hybrid watermark from the pirated copy. The extracted information helps them identify the source of the leak, such as the specific theater or distribution channel from which the illegal recording originated. They can then take appropriate legal action against the perpetrators and work towards preventing future piracy attempts.
Note
By employing hybrid watermarking, CinemaWorks can protect their intellectual property, deter piracy, and maintain the integrity of their feature films, ensuring a fair and secure distribution process.
2.1.4
Reversible Watermarking
Reversible watermarking, also known as lossless or invertible watermarking, allows for the complete restoration of the original host image or video after the watermark extraction process. This technique is particularly useful in applications where the integrity of the original content is crucial, such as medical imaging and forensic analysis [4].
Interesting
Example: Reversible Watermarking for Medical Imaging
In the healthcare industry, medical imaging plays a vital role in diagnosing and treating patients. Imaging modalities such as X-rays, CT scans, and MRIs generate high-quality digital images that are used for accurate analysis and decision-making. However, these medical images often contain sensitive patient information that must be protected from unauthorized access and tampering.
To address this challenge, healthcare institutions implement reversible watermarking techniques. Reversible watermarking allows the embedding of a watermark into the medical image without any permanent alteration to the original pixel values. The watermark contains essential metadata, such as the patient's identification number, the date and time of the imaging procedure, and the name of the healthcare provider.
When the watermarked medical image is stored in the hospital's database or transmitted to other healthcare professionals, the watermark remains embedded in the image. This ensures the authenticity and integrity of the medical data, preventing any unauthorized modifications or tampering.
However, when the medical image needs to be analyzed for diagnostic purposes, the reversible watermark can be extracted, restoring the image to its original pixel values. This is crucial because any alterations to the image data could potentially lead to misdiagnosis or improper treatment.
Note
Furthermore, if there is a breach in the hospital's database and the medical images are accessed by unauthorized individuals, the reversible watermark can help trace the origin of the breach. The watermark information can identify the specific patient, the healthcare provider, and the timestamp associated with the compromised image, aiding in the investigation process.
+
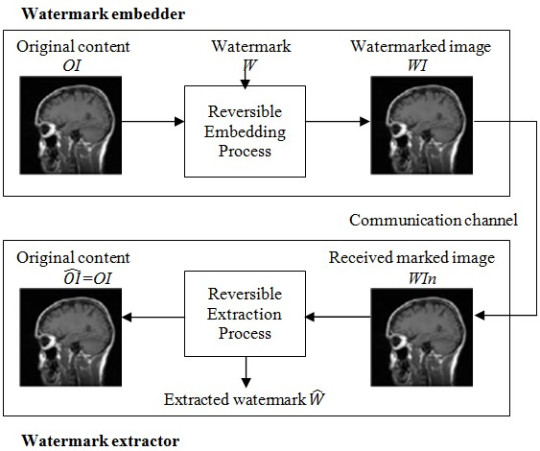
Fig. 7: General block diagram of reversible watermarking technique
By utilizing reversible watermarking, healthcare institutions can ensure the security, integrity, and privacy of medical images while maintaining the ability to restore the original image data when necessary.
+
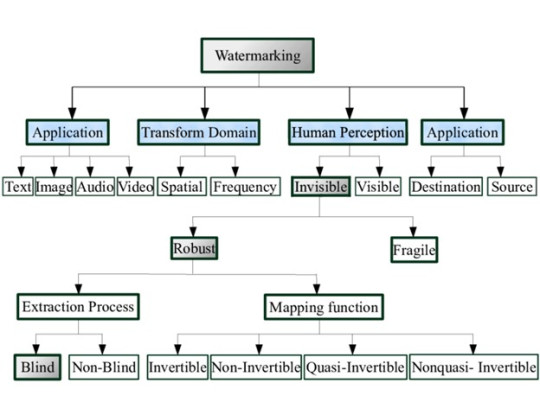
Fig. 8: Visual representation of different types of watermarking techniques