1.1
Host-based Intrusion Detection Systems
Interesting
Specifically, HIDS monitor data like traffic information, system logs, and audit trails to determine if a system has been compromised. This approach relies on hosts monitoring the devices and detecting improper use of available resources.
Typically, HIDS have agents installed on hosts that monitor activity and forward data to management servers, as depicted in Figure 2. HIDS can also use special devices to run the software agent directly and monitor traffic. In some ways, these devices can be considered a form of NIDS designed to protect specific elements:
- Client Host: Agents designed to observe user hosts monitor the operating system (OS) and common applications, such as web browsers or email clients.
- Application Service: Some agents, also known as application-based IDS, are tailored to monitor specific applications, such as a web server or database server programs.
+
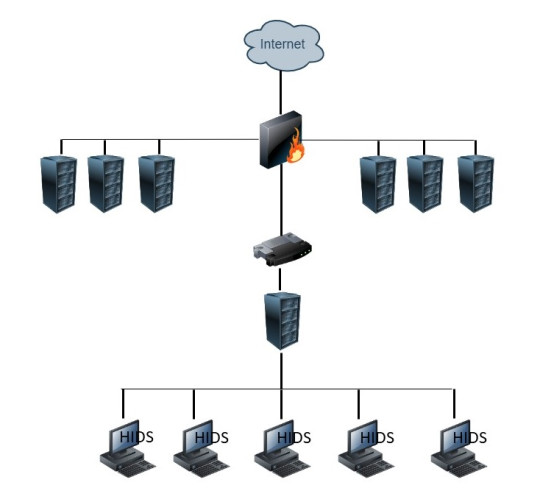
Fig. 2. HIDS example
Interesting
Note
Definition
Its main functionalities include log analysis, integrity checking, Windows registry monitoring, rootkit detection, real-time alerting, and active response.
Interesting
Definition
Interesting
The main advantages of Tripwire are its detailed monitoring and reporting capabilities.
Definition
Wazuh is an open source security monitoring platform that integrates different security functions, including intrusion detection, log management, and alerting of security events and incidents.
Interesting
The main advantages of Wazuh are its ability to combine multiple security functionalities in one platform, including host-based intrusion detection, and its use of powerful visualization and analysis tools.
Definition
SolarWinds Security Event Manager is a commercial solution that offers automated threat detection and response, centralized log management, and an intuitive dashboard.
Interesting
The main advantages of SolarWinds Security Event Manager are its wide range of security information and event management functionalities, user-friendly interface with easy setup and configuration, and its ability to handle large volumes of logs and events.